
Spear phishing attacks are nothing new, but the tactics used by cybercriminals continue to evolve. It can be difficult to detect spear-phishing attacks, as they often use information that is specific to the target.
Don’t worry, ZZ Computer will provide you with the five common spear-phishing tricks that you need to watch out for! Before that, what is spear phishing?
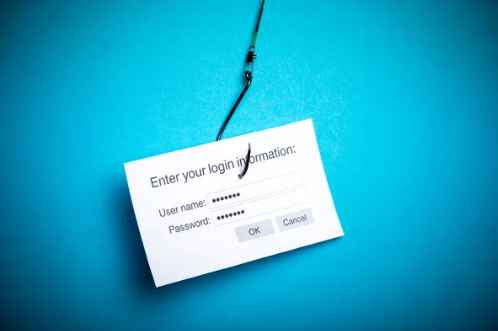
Targeted attacks in which attackers send emails to specific persons or groups inside an organization in order to steal sensitive data are known as spear-phishing attacks. These emails frequently include a malicious link that, when clicked, installs malware onto the user’s computer.
Do you understand what a spear-phishing attack entails? If you don’t, you aren’t alone. Many people are unfamiliar with the principles of these types of attacks. We’ll go over spear-phishing strategies and how they’re carried out in this part.
You should be wary of the following spear-phishing strategies:
An email harvesting attack is one of the most prevalent techniques for attackers to obtain access to credentials. This entails collecting emails from publicly available sources and then sending spear-phishing emails. This method is frequently used to target high-profile people or organizations.
One of the most prevalent spear-phishing attacks is this one. It entails sending fake emails that look to come from a reliable source, such as a coworker or a company executive. This method is frequently used to persuade victims to share sensitive information or click on malicious links.
Many spear-phishing attempts make use of social media to obtain information or personal information about the victim. This can be accomplished by creating bogus internet profiles, extracting personal information from public profiles, or persuading victims to divulge sensitive data.
Egress filtering is used by many businesses to safeguard their networks against harmful activities. Attackers, on the other hand, can take advantage of this by sending corrupted packets through these monitoring systems. This makes it easier for them to carry out their spear-phishing attacks and obtain information without being discovered. This information will be used for nefarious purposes.

Cybercriminals are always looking for new ways to scam people and companies out of their money or personal information. While phishing attacks can come in all shapes and sizes, here are five of the most common spear-phishing techniques that you need to watch out for.
A spoofed email is one of the most popular types of spear-phishing assaults. This frequently entails sending malicious emails that look to come from a reliable source. These malicious emails may include harmful attachments or URLs that might infect your computers.
CEO fraud scams are another sort of spear-phishing attack. This involves attackers sending emails that appear to be from a company boss, seeking money or confidential information from the victim.
Urgent requests for money transfers, ambiguous or suspicious wording, unrealistic timeframes, and requests for personal details such as login credentials are all examples.
A Business Email Compromise (BEC) is what many spear phishers are actively trying to create. This type of attack uses an impersonated, spoofed, or hacked corporate email account to trick employees into wire transfer payments or sharing confidential information. Spear phishing is a sophisticated form of phishing that targets specific individuals or organizations. The attackers do their homework by researching their victims and crafting personalized messages that appear to be from a trusted source.
Spear phishers often use the same email address for multiple attacks, making it easy to spot BEC attempts in your inbox. If you receive an email that looks suspicious, do not click on any links or attachments. Instead, forward the message to your IT department or security team for analysis. By being vigilant, you can help to protect your organization from falling victim to a costly BEC attack.
In a spear-phishing email, attackers will try to get you to click on a malicious link that will take you to a fake website. This fake website may look identical to a legitimate website, but it will be used for malicious purposes mainly to gather your personal information.
Other times, spear phishing messages will include malicious attachments in their emails. These malicious attachments may contain viruses or other malware that can infect your computer if you open them.
A common spear-phishing email tactic is to request sensitive data from the victim. This may include your Social Security number, bank account information, or credit card number.
Spear phishers may pose as a credible organization, such as your bank, and try to trick you into sharing this confidential information. They may also use urgent request tactics to try to get you to comply with their demands.
Phishing, spear-phishing, and whaling assaults are various forms of cybercrime that entail duping someone into handing over sensitive information. While they all use similar techniques, these three types of attacks have significant key differences.
Don’t worry; we’ll go over each one and discuss how to protect yourself from them. Watch this space!
When it comes to phishing VS spear-phishing VS whaling, the main difference is the target. The target is what distinguishes spear phishing from normal phishing. Spear phishing is a more targeted attack than phishing, which targets a bigger number of people. It involves phishing by voice or SMS.
The message content in spear-phishing emails is typically tied to a time-sensitive event, such as a natural disaster. This instills a sense of urgency in the victim, prompting them to act without hesitation.
Spear phishing definition – when a cybercriminal impersonates a specific person or organization to dupe the victim into giving sensitive information. The attacker’s goal is to gain access to the victim’s confidential data, such as login credentials or financial information.
Spear phishing attacks are more sophisticated than regular phishing attacks and can be very difficult to spot.
The term “whale” is used to describe high-profile individuals, such as corporate executives or celebrities. Whaling attacks are spear-phishing assaults that target high-ranking executives such as CEOs, CFOs, and other executives.
Phishing emails are commonly used in these attacks, with the attacker impersonating an executive and requesting confidential information or cash.

As we can see, spear phishers are a serious threat to businesses and individuals alike. By taking the proper precautions, you can help protect yourself and your organization from these malicious attacks.
If you think you may be the target of a spear-phishing attack, or if you have any concerns about the security of your data, contact ZZ computer services immediately. Our team of security experts can help you assess your risks and take the necessary steps to protect your data.
We hope you found this article helpful. Stay tuned for more blog posts on cybersecurity threats and how to defend against them. See our complete guide to Cybersecurity for Small Businesses in Los Angeles here.
We firmly believe that the internet should be available and accessible to anyone, and are committed to providing a website that is accessible to the widest possible audience, regardless of circumstance and ability.
To fulfill this, we aim to adhere as strictly as possible to the World Wide Web Consortium’s (W3C) Web Content Accessibility Guidelines 2.1 (WCAG 2.1) at the AA level. These guidelines explain how to make web content accessible to people with a wide array of disabilities. Complying with those guidelines helps us ensure that the website is accessible to all people: blind people, people with motor impairments, visual impairment, cognitive disabilities, and more.
This website utilizes various technologies that are meant to make it as accessible as possible at all times. We utilize an accessibility interface that allows persons with specific disabilities to adjust the website’s UI (user interface) and design it to their personal needs.
Additionally, the website utilizes an AI-based application that runs in the background and optimizes its accessibility level constantly. This application remediates the website’s HTML, adapts Its functionality and behavior for screen-readers used by the blind users, and for keyboard functions used by individuals with motor impairments.
If you’ve found a malfunction or have ideas for improvement, we’ll be happy to hear from you. You can reach out to the website’s operators by using the following email
Our website implements the ARIA attributes (Accessible Rich Internet Applications) technique, alongside various different behavioral changes, to ensure blind users visiting with screen-readers are able to read, comprehend, and enjoy the website’s functions. As soon as a user with a screen-reader enters your site, they immediately receive a prompt to enter the Screen-Reader Profile so they can browse and operate your site effectively. Here’s how our website covers some of the most important screen-reader requirements, alongside console screenshots of code examples:
Screen-reader optimization: we run a background process that learns the website’s components from top to bottom, to ensure ongoing compliance even when updating the website. In this process, we provide screen-readers with meaningful data using the ARIA set of attributes. For example, we provide accurate form labels; descriptions for actionable icons (social media icons, search icons, cart icons, etc.); validation guidance for form inputs; element roles such as buttons, menus, modal dialogues (popups), and others. Additionally, the background process scans all of the website’s images and provides an accurate and meaningful image-object-recognition-based description as an ALT (alternate text) tag for images that are not described. It will also extract texts that are embedded within the image, using an OCR (optical character recognition) technology. To turn on screen-reader adjustments at any time, users need only to press the Alt+1 keyboard combination. Screen-reader users also get automatic announcements to turn the Screen-reader mode on as soon as they enter the website.
These adjustments are compatible with all popular screen readers, including JAWS and NVDA.
Keyboard navigation optimization: The background process also adjusts the website’s HTML, and adds various behaviors using JavaScript code to make the website operable by the keyboard. This includes the ability to navigate the website using the Tab and Shift+Tab keys, operate dropdowns with the arrow keys, close them with Esc, trigger buttons and links using the Enter key, navigate between radio and checkbox elements using the arrow keys, and fill them in with the Spacebar or Enter key.Additionally, keyboard users will find quick-navigation and content-skip menus, available at any time by clicking Alt+1, or as the first elements of the site while navigating with the keyboard. The background process also handles triggered popups by moving the keyboard focus towards them as soon as they appear, and not allow the focus drift outside of it.
Users can also use shortcuts such as “M” (menus), “H” (headings), “F” (forms), “B” (buttons), and “G” (graphics) to jump to specific elements.
We aim to support the widest array of browsers and assistive technologies as possible, so our users can choose the best fitting tools for them, with as few limitations as possible. Therefore, we have worked very hard to be able to support all major systems that comprise over 95% of the user market share including Google Chrome, Mozilla Firefox, Apple Safari, Opera and Microsoft Edge, JAWS and NVDA (screen readers), both for Windows and for MAC users.
Despite our very best efforts to allow anybody to adjust the website to their needs, there may still be pages or sections that are not fully accessible, are in the process of becoming accessible, or are lacking an adequate technological solution to make them accessible. Still, we are continually improving our accessibility, adding, updating and improving its options and features, and developing and adopting new technologies. All this is meant to reach the optimal level of accessibility, following technological advancements. For any assistance, please reach out to