There are advantages and disadvantages to Managed Security IT services. And one of the most common tackled disadvantages of Managed Security is that its ability to get complex.
How can complexity be a problem?
When your technology has become complex it might be hard for you to get the best out of your business. This means that you cannot properly use or set up your projects, data, and information on your tech devices due to its difficult process. And this is the most common scenario for those who just hire someone from their company to set up managed security services.
On the other hand, managed security’s complexity has its advantages. Managed Security will allow you to ensure the protection of your data and business information that you wouldn’t want to get hacked.
As a matter of fact, managed security gives holistic security from threats and hackers. You may think it’s kinda expensive but we, ZZ computer, can offer reasonable pricing for you.
In the IT world, data security becomes a necessary element of a company. Data security is always paired or joined with a cloud system to centralized all data and information to a system source. However, many of the security risks from cloud systems are not caused by the system itself but because of human negligence or error.
Cloud configurations are the most common problems that cause harm to the sensitive data of every company. As a matter of fact, according to IBM and Ponemon Institute, data breached always happen for nearly one-fifth of data breaches they have encountered.
Now, the question is: how to beat complexity problems when availing managed security?
Confidential Computing encrypts data that can be concocted in limited memory access in order to ensure data confidentiality. This is a concept that is specifically useful for public clouds or clouds with many users.
Moreover, confidential computing allows you to focus on software and hardware-based security against security threats and risks that can be compromised. This confidential computing has always gained popularity in terms of business priorities because it increases the chance of getting a sense of security upon your confidential business data or information.
Another way to beat the complexity problem of managed security is to build a comprehensive cloud security strategy that expands your processes and defines or makes clear guidelines for all cloud resources.
In this way, every work process will be organized and there will be fewer possible threats.
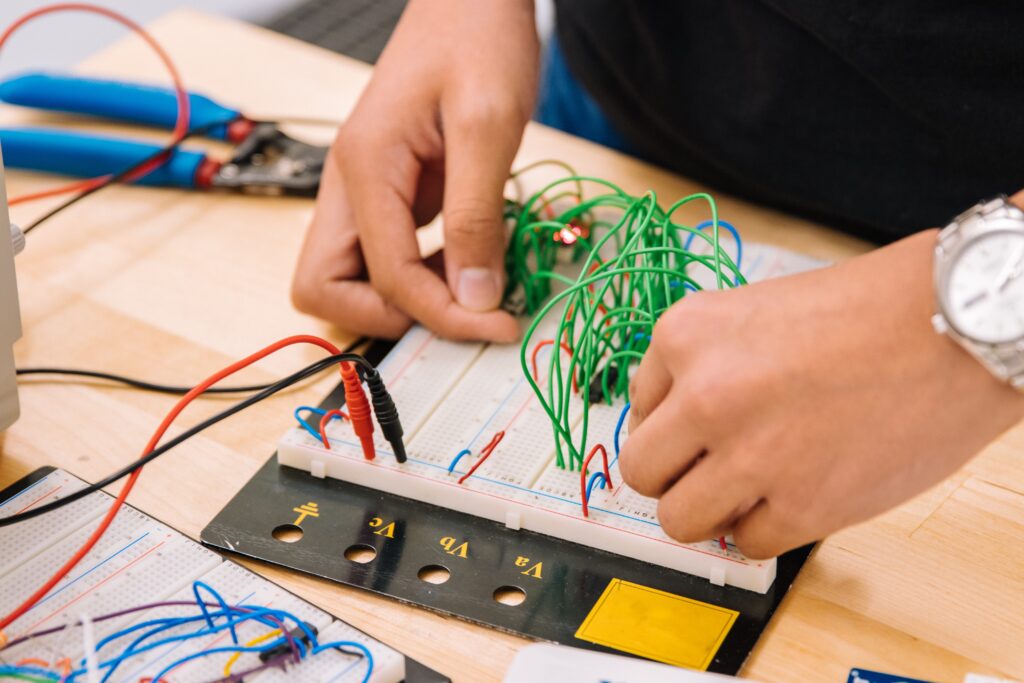
To ensure that technology complexity won’t affect your managed security, it is best to select the best IT architecture. What does this mean? It means that identifying your sensitive data and ensure that your privacy policies are well-placed, including those hardware tools. Also, it’s best to review your current technical problems and goals. And through these, you create your IT Architecture or IT planning in terms of the right positioning and wiring of your technologies.
Remember, with excellent IT Architecture or planning, technology complexity won’t affect the processes. In fact, everything will be easier for you.
This may sound cliché but nothing beats the importance of partnering with an experienced IT Services Provider such as ZZ Computer.
Partnering with an experienced IT Provider is crucial because, with a very technical problem, you wouldn’t want anything to end up into a waste of money if your security problem won’t get resolve.
That is why it’s better to choose expert in cybersecurity service that has been giving IT Services to Los Angeles Companies.
To beat the complexity of managed security and other IT-related services, it’s best to apply the given tips above. With that, you don’t only beat its complex process but also get a better chance of being successful by having a protected data and information and speedy business processes.
We firmly believe that the internet should be available and accessible to anyone, and are committed to providing a website that is accessible to the widest possible audience, regardless of circumstance and ability.
To fulfill this, we aim to adhere as strictly as possible to the World Wide Web Consortium’s (W3C) Web Content Accessibility Guidelines 2.1 (WCAG 2.1) at the AA level. These guidelines explain how to make web content accessible to people with a wide array of disabilities. Complying with those guidelines helps us ensure that the website is accessible to all people: blind people, people with motor impairments, visual impairment, cognitive disabilities, and more.
This website utilizes various technologies that are meant to make it as accessible as possible at all times. We utilize an accessibility interface that allows persons with specific disabilities to adjust the website’s UI (user interface) and design it to their personal needs.
Additionally, the website utilizes an AI-based application that runs in the background and optimizes its accessibility level constantly. This application remediates the website’s HTML, adapts Its functionality and behavior for screen-readers used by the blind users, and for keyboard functions used by individuals with motor impairments.
If you’ve found a malfunction or have ideas for improvement, we’ll be happy to hear from you. You can reach out to the website’s operators by using the following email
Our website implements the ARIA attributes (Accessible Rich Internet Applications) technique, alongside various different behavioral changes, to ensure blind users visiting with screen-readers are able to read, comprehend, and enjoy the website’s functions. As soon as a user with a screen-reader enters your site, they immediately receive a prompt to enter the Screen-Reader Profile so they can browse and operate your site effectively. Here’s how our website covers some of the most important screen-reader requirements, alongside console screenshots of code examples:
Screen-reader optimization: we run a background process that learns the website’s components from top to bottom, to ensure ongoing compliance even when updating the website. In this process, we provide screen-readers with meaningful data using the ARIA set of attributes. For example, we provide accurate form labels; descriptions for actionable icons (social media icons, search icons, cart icons, etc.); validation guidance for form inputs; element roles such as buttons, menus, modal dialogues (popups), and others. Additionally, the background process scans all of the website’s images and provides an accurate and meaningful image-object-recognition-based description as an ALT (alternate text) tag for images that are not described. It will also extract texts that are embedded within the image, using an OCR (optical character recognition) technology. To turn on screen-reader adjustments at any time, users need only to press the Alt+1 keyboard combination. Screen-reader users also get automatic announcements to turn the Screen-reader mode on as soon as they enter the website.
These adjustments are compatible with all popular screen readers, including JAWS and NVDA.
Keyboard navigation optimization: The background process also adjusts the website’s HTML, and adds various behaviors using JavaScript code to make the website operable by the keyboard. This includes the ability to navigate the website using the Tab and Shift+Tab keys, operate dropdowns with the arrow keys, close them with Esc, trigger buttons and links using the Enter key, navigate between radio and checkbox elements using the arrow keys, and fill them in with the Spacebar or Enter key.Additionally, keyboard users will find quick-navigation and content-skip menus, available at any time by clicking Alt+1, or as the first elements of the site while navigating with the keyboard. The background process also handles triggered popups by moving the keyboard focus towards them as soon as they appear, and not allow the focus drift outside of it.
Users can also use shortcuts such as “M” (menus), “H” (headings), “F” (forms), “B” (buttons), and “G” (graphics) to jump to specific elements.
We aim to support the widest array of browsers and assistive technologies as possible, so our users can choose the best fitting tools for them, with as few limitations as possible. Therefore, we have worked very hard to be able to support all major systems that comprise over 95% of the user market share including Google Chrome, Mozilla Firefox, Apple Safari, Opera and Microsoft Edge, JAWS and NVDA (screen readers), both for Windows and for MAC users.
Despite our very best efforts to allow anybody to adjust the website to their needs, there may still be pages or sections that are not fully accessible, are in the process of becoming accessible, or are lacking an adequate technological solution to make them accessible. Still, we are continually improving our accessibility, adding, updating and improving its options and features, and developing and adopting new technologies. All this is meant to reach the optimal level of accessibility, following technological advancements. For any assistance, please reach out to